Data Protection
Data handled by Mercari Group (including the personal information of customers) is protected in accordance with industry best practices.
Secure Design and Secure Programming
Security Requirements Consulting
Our team works closely with stakeholders to define security requirements for our products. We encourage all employees to consult with our Security team and get advice on any questions or concerns they may have.
Product Security Practices
New features, large changes in functionality, and major releases undergo a security review process by our Product Security team. The team is involved from the initial stages of the software development lifecycle, to ensure the quality and security of our services throughout every stage of their development. In addition to design reviews, we augment our security reviews through code reviews and tools to automatically test our applications for vulnerabilities, such as SAST (Static Application Security Testing), DAST (Dynamic Application Security Testing), and SCA (Software Composition Analysis) tooling.
Secure Coding Best Practices
To ensure the quality and security of our applications, our Security team maintains internal secure coding training and a Security Champion Program based on industry best practices.
Security Testing
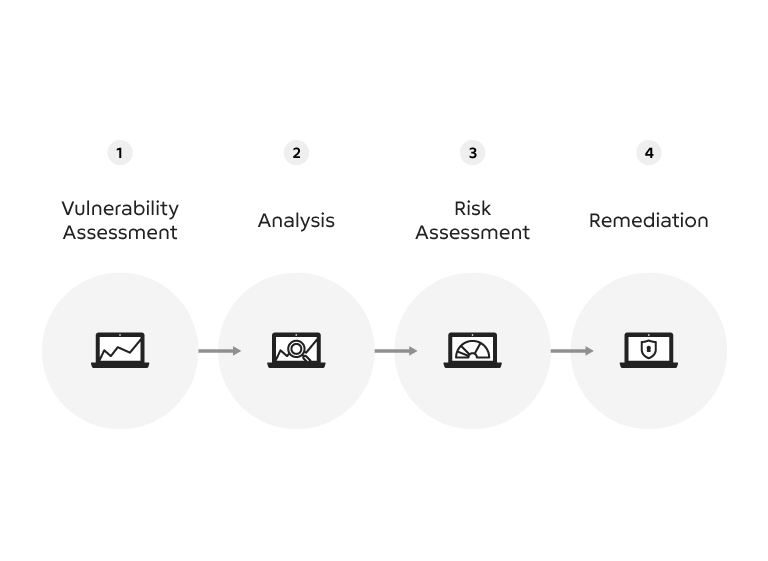
Automated Security Tooling
The Product Security team maintains tooling for frequent static and dynamic analysis of applications to detect potential vulnerabilities.
Third-Party Assessment
To refine our incident response process and detection capabilities and identify potential issues from an objective perspective, we periodically engage in red team exercises conducted by third parties.
Security Training
In-house Security Training
Our annual training initiatives include mandatory information security and privacy training for all employees and secure coding training for all engineers to ensure best security practices are incorporated throughout the development lifecycle.
The Security team also provides various e-learning courses tailored to specific roles through the company’s learning management system.
Security Champion Program
In addition to our in-house security training programs, our engineers are encouraged to participate in our Security Champion Program. The program enables participants to build hands-on security experience and integrate security best practices into daily operations, empowering them to take greater responsibility for the security of their domains.
Threat Monitoring and Handling
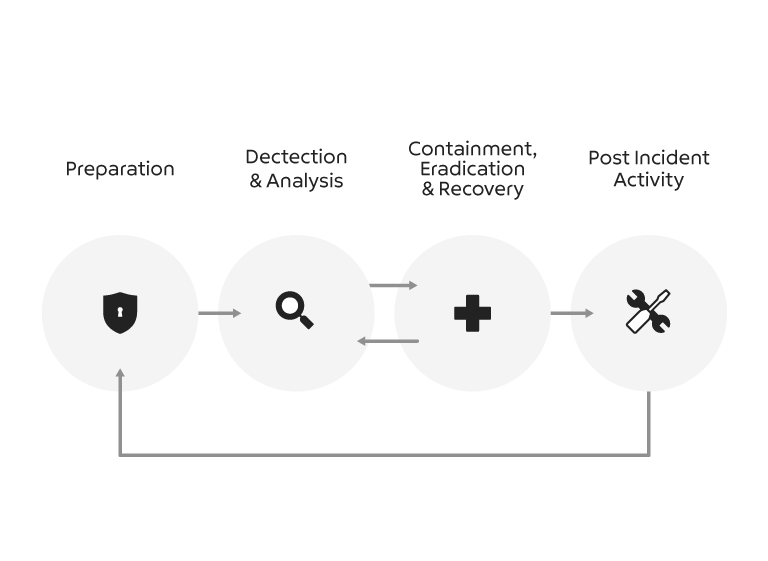
Detection and Monitoring
The Security team monitors systems for various indicators of attack, such as unauthorized access attempts and malware infection. The team responds promptly to significant security events and conducts a thorough investigation of potential threats.
A Security Orchestration, Automation, and Response (SOAR) tool (developed and maintained in-house) is used to centralize, monitor, and respond to alerts allowing us to adapt and respond to threats rapidly.
Incident Response
We maintain an incident response process, playbooks, and relevant documentation to ensure prompt and effective incident management.
The Mercari Group is a member of the Nippon CSIRT Association and the Forum of Incident Response and Security Teams (FIRST).
Phishing Countermeasures
Protecting our users from phishing attacks is key to ensuring the safety and security of our services
We work with external organizations and have countermeasures in place to promptly take down phishing sites.
Collaboration With External Organizations
Nippon CSIRT Association (NCA)
Forum of Incident Response and Security Teams (FIRST)
Keidanren Cybersecurity Working Group
Open ID Foundation Japan
FIDO Alliance
International Association of Privacy Professionals (IAPP) – Bronze Sponsor
